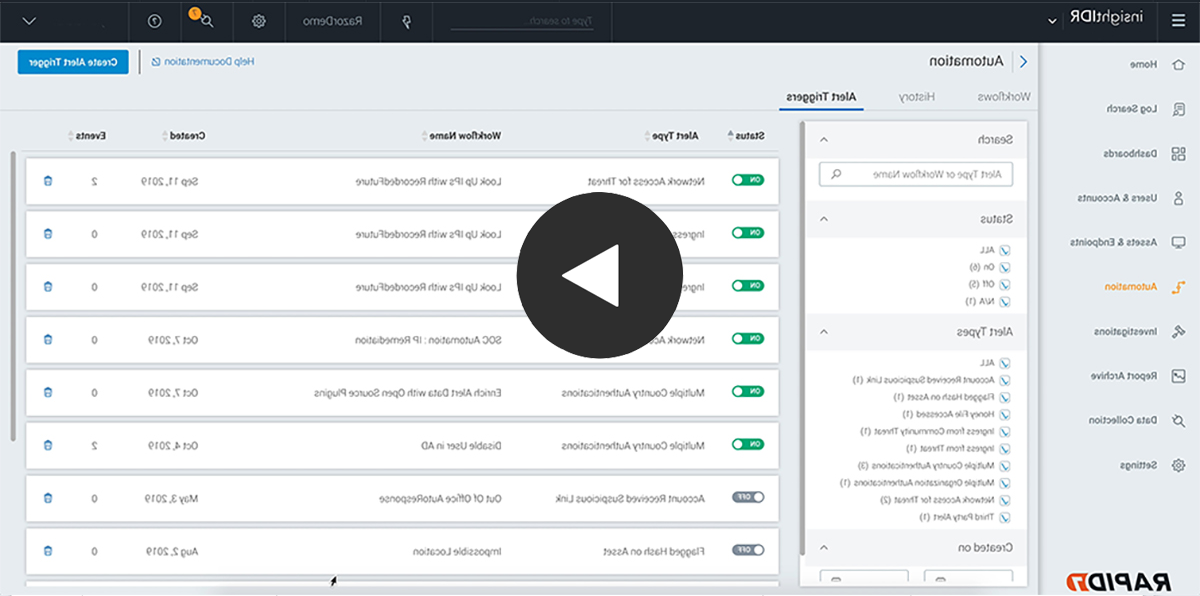
Automate repetitive security tasks
Multiple automation workflows allow you to respond to security events as they emerge on your network. You can configure these workflows to automate all the manual drudgery that can dominate your day.
依赖于预构建的工作流
Insight印尼盾 has prebuilt workflows for containing threats on an endpoint, 暂停用户帐户, 和 integration with ticketing systems.
You’ll see enrichment via open source threat intelligence added to this list of workflows, as well as the ability to trigger any of these workflows (or seamlessly integrated InsightConnect workflows) off of alerts.
It’s easy to kick off any workflow or response playbook with the click of a button. And with expert response suggestions built into our detections library, you’ll know what to do faster.
Get critical use cases out-of-the-box
When investigating threats in Insight印尼盾, you not only get important context, but you can take immediate steps to contain or respond to a threat. 例如, Insight Agent, you can kill malicious processes or quarantine infected endpoints from the network. You can also use Insight印尼盾 to take containment actions across Active 导演y, 访问管理, 功能, 防火墙工具.
Provision 和 deprovision user accounts
Whenever you get an alert in Insight印尼盾, notable user 和 asset behavior is shown on a visual investigation timeline. Not only do you have the necessary context to make a decision regarding a user account, but you can take action directly from an investigation to contain the threat. 支持ed vendors include Active 导演y 和 Okta for user-level containment.
自动充实警报
Enrich investigations 和 User Behavior Analytics alerts with open-source or supported threat intelligence feeds through prebuilt workflows in Insight印尼盾, or via InsightConnect for even more extensibility.
Customize automation with InsightConnect
Streamline 和 accelerate highly manual, time-intensive, processes 24 hours a day. across IT 和 Security cloud apps, on-premise systems, employees, 和 administrators.
With more than 300 plugins to connect your IT 和 security systems — 和 a library of customizable workflows — you’ll free up your security team to tackle the serious challenges only they can. And when you build your own rich workflows, there’s low-to-no coding involved.